The threat of cybercrime is the new reality for enterprises worldwide.
It is not a matter of if you will be targeted, but a matter of when. Unfortunately, most organizations are not proactive in their approach to information security until they have been breached. Herjavec Group has practical experience addressing and managing the most complex security breaches. Through timely and strategic response to security incidents, Herjavec Group reduces recovery time, costs and damage.

HG Digital Forensics & Incident Response Services can be leveraged on an emergency basis, or as an integral part of your proactive cybersecurity program through our HG IR Retainers. Not only does an HG IR Retainer complement the resolver group initiation in our HG MSS offering, pending the remediation required, but it provides peace of mind and accelerated response times for expert-level support when your enterprise needs it most.
Experience HG Incident Response Services
Why Trust HG To Lead Your Incident Response?
- When an incident occurs, we respond with a customized response team.
We bolster your existing tools and processes with our state-of- the-art networking, discovery, and forensic tools. Our flexibility provides a faster, more effective response. We maintain a neutral perspective throughout our response delivery. - We are on-site offering a high-touch response.
While we can provide remote triage and expertise across multiple security domains, we believe that on-site presence
is critical to managing an incident, interacting with management and ensuring the best outcome overall. - We do not abandon you once the incident is closed.
When a complex incident occurs, Herjavec Group follows through on recommendations that are made and supports you through the entire cycle of remediation as required. This includes providing you with the consultation and technical expertise needed throughout the remediation process. - Our retainer hours are flexible and can be dedicated to additional incident response cybersecurity services.
Rest assured knowing that your investment with HG can be leveraged for Incident Response support as needed or dedicated to additional Incident Response services, such as tabletop exercises and Incident Response planning.
HG Incident Response Process
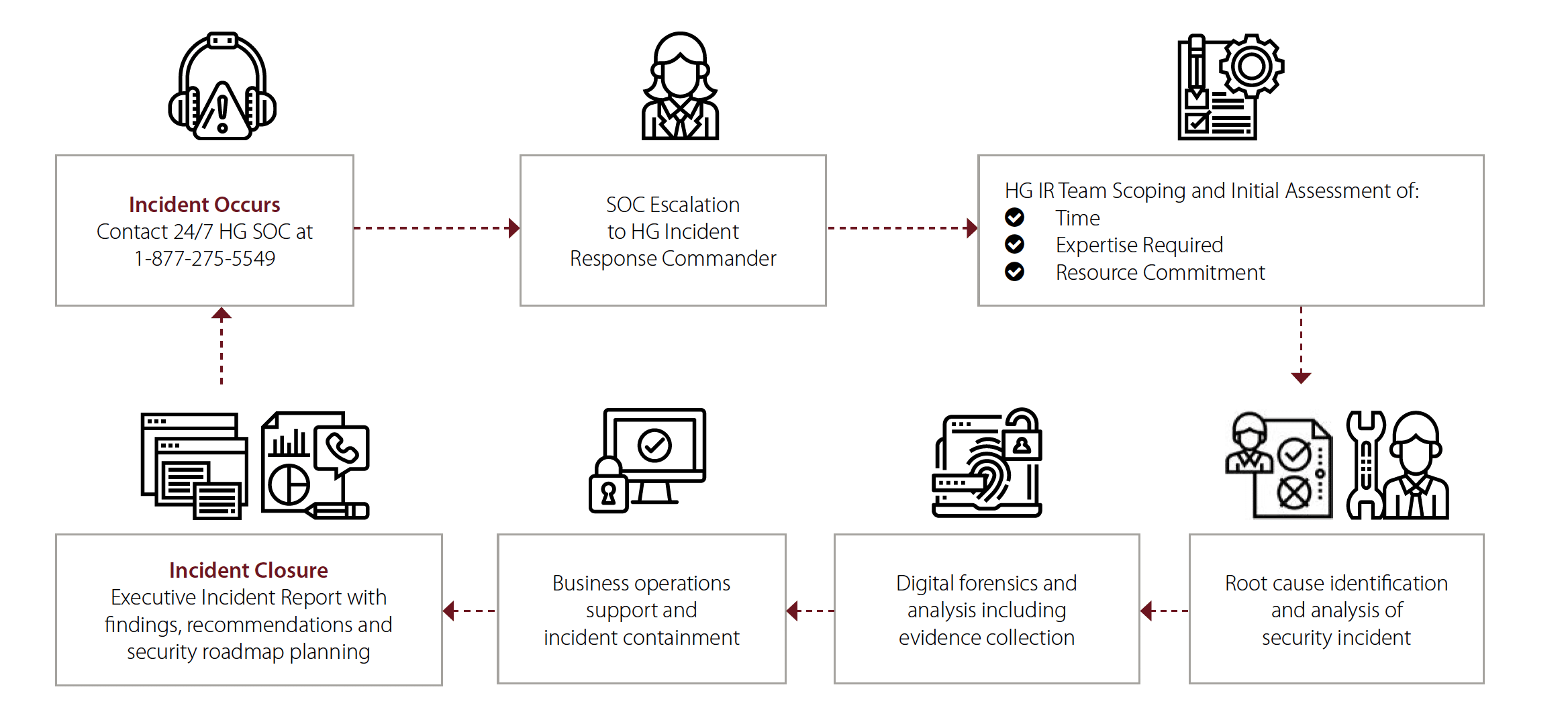
Modeled after NIST SP800-61r2 and ISO 27035,
Herjavec Group’s Incident Response team supports four activity phases:
![]()
Scoping
Detection & analysis
![]()
Incident response
Containment, evidence collection,
eradication or remediation
![]()
Recovery
Support in return to
normal operations
![]()
Post Incident Review
Including controls reviews,
actions for improvement
3-Tiered Incident Support Structure
![]()
Incident Commander
Your first point of contact to understand the scale and scope of the incident.
In contact with you and incident controller daily to understand status and
support the team daily.
![]()
Incident Controller
On-site resource responsible for tracking activities and providing daily reporting on the progress of the incident handling.
![]()
Incident Handler
The resources working on the incident itself. Specifically selected based on their skill and experience. The skills include incident detection/ analysis, incident control/ handling, containment, eradication/recovery, and forensic investigation/root cause analysis.
Plan for Security Incidents with an Incident Response Retainer
-
Ultimate flexibility – retainer packages can be dedicated to additional HG services such as Table Top Exercises, Incident Response Planning and Advisory Services
-
Budgeted line item with no surprises
-
Shortened SLA’s for Incident Response
-
Seamless transition and collaboration between HG MDR, HG Threat and HG SOC experts supporting your HG Managed Security Service
-
Coordinated program alignment in advance to save time and resource when you need it most
Customer Success Story
SUCCESSFUL EXECUTION OF TABLE-TOP EXERCISES IN A COMPLEX ENVIRONMENT
Challenges Addressed:
- Customer required Incident Response training and drill practices without impacting business operations.
- Unaware of various cyber attack possibilities, threat actor motivations and techniques.
Industry Frameworks Leveraged:
- ISO/IEC 27000 Series (ISO 27035-1 and 27035-2)
- NIST Cybersecurity Framework
- SANS Institute Incident Response Methodology
How We Delivered
- Table-top exercises where the internal customer security team is guided through simulated real-world security incidents
- HG provided real-world cyber attack scenarios including data exfiltration, ransom demands and extortion and blended cyber theory about the Dark Web (Deep vs. Dark), Bitcoin cryptocurrency, etc.
- A detailed post-exercise report with qualitative assessment and roadmap recommendations for development
“Within 12 hours we had Herjavec Group on-site helping us troubleshoot, taking control of the situation, and helping us with an incident response management plan.”
VP of Technology, Goldcorp
Examples of the Incident Response security support offered to Goldcorp include:
- Managed and monitored the customer’s incident bridge
- Isolated the network from external threats
- Disrupted communication channels used by threat actors
- Architected security strategy involving Firewalls, IPS, SIEM, Anti-Virus, and APT appliances
- Deployed all of the security technologies for remediation response
- Developed custom reporting to highlight indicators of compromise
- Provided technical consulting across multiple levels of the organization
- Co-ordinated service restoration to key business functions
- Guided the business on security incident response and remediation strategies
Additional Incident Response &
Emergency Preparedness Services
RESPONSE READINESS
A two-day on-site service to assist you in building an Incident Response plan. Herjavec Group will be on-site to review your current state IR plans and make recommendations for improvement. When used bi-annually, Herjavec Group can assist your organization in creating a formal Incident Response plan.
POST-INCIDENT EXECUTIVE BRIEFING
A one-day session with the Incident Commander, or a Herjavec Group executive, to talk to your team’s senior staff about the incident. HG must have been involved in the IR engagement resolution. In the Post-Incident Executive Briefing, Herjavec Group will review the incident details, the incident handling process, and share recommendations for improvements to your process of incident handling.
Preparing for an Incident
A cyber attack is one of the biggest threats
to your business.
As a security professional, you’re balancing technology investment, internal process and access controls – but does your proactive defense include a comprehensive incident response plan
Learn more about how your organization can prepare for a cyber incident and mitigate the impacts following an event to maintain business continuity, by downloading our full guide.
